
Pushing vs. Pulling in the Arm Action – Grant's Training Blog
4.5
(486) ·
$ 7.50 ·
In stock
Description

CVE-Vulnerability-Information-Downloader - Downloads Informa - vulnerability database
sample_code_2016/scrape_insert_wordpress/company_data_FULL_1468846551.json at master · robert-boersig/sample_code_2016 · GitHub

How Akamai Can Help You Fight the Latest Exploitation Attemp - vulnerability database

Screening + Explaining Pushing Ball into Release
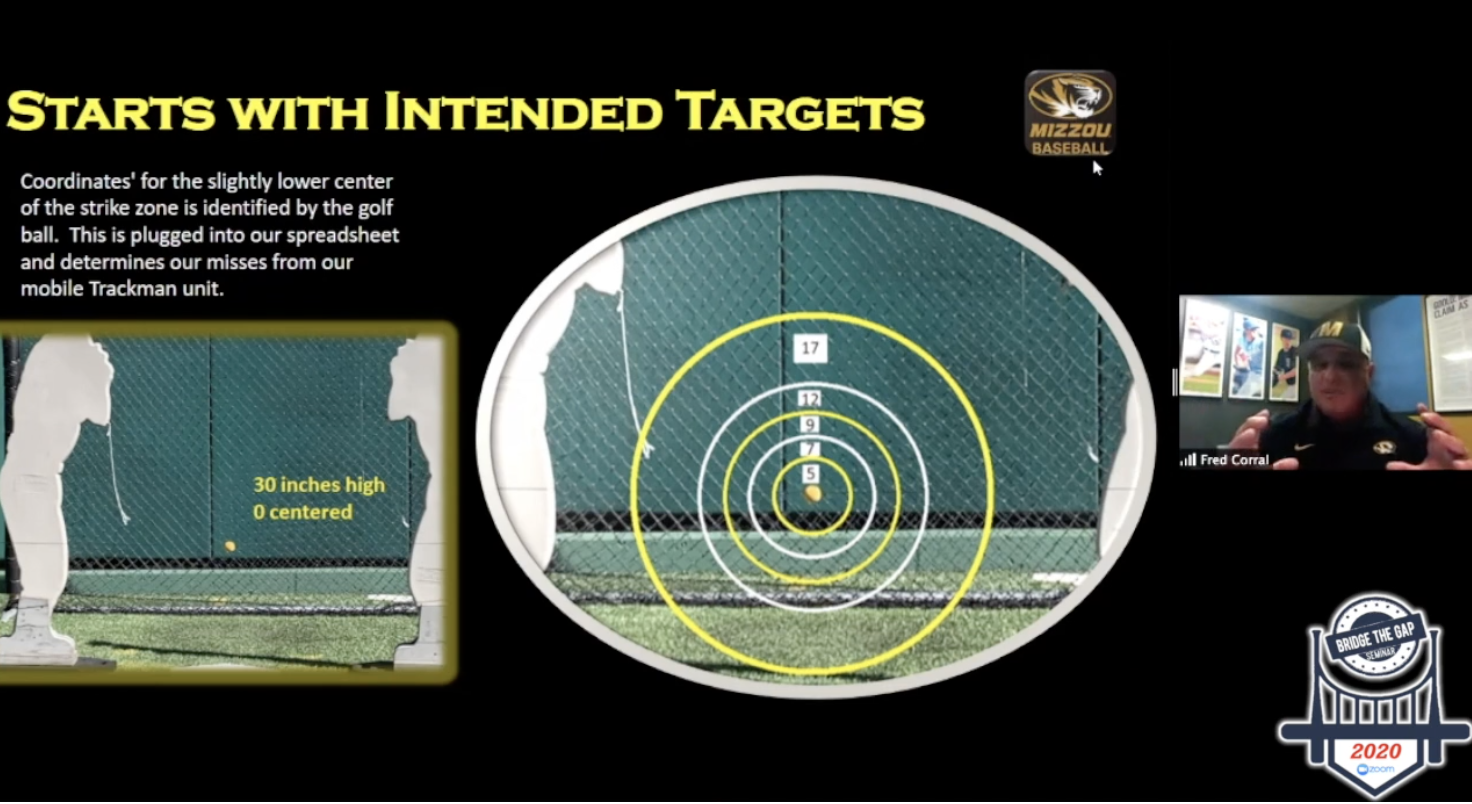
Movement, Command, & Creating a Competitive Advantage: Recapping BTG20 Part II
stocknet-code/res/vocab.txt at master · yumoxu/stocknet-code · GitHub

State-Sponsored Hackers Likely Exploited MS Exchange 0-Days - vulnerability database

Arm Action: What Is It, and How to Improve It

Arm Action: What Is It, and How to Improve It
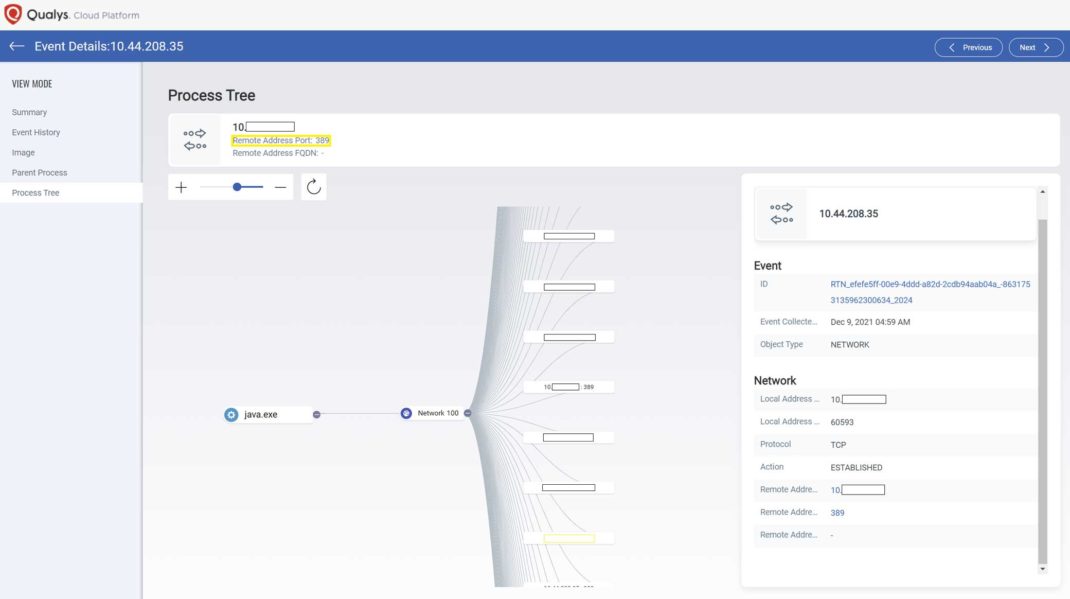
Log4Shell Exploit Detection and Response with Qualys Multi-V - vulnerability database
Related products
You may also like
copyright © 2019-2024 richy.com.vn all rights reserved.